Right off the bat, we’re here to tell you that anyone promising you a sure-shot solution to all your CMMC woes is trying to pull a fast one on you. The Cybersecurity Maturity Model Certification (CMMC) is a comprehensive move by the U.S. Department of Defense (DoD) that involves many moving parts and will take years to implement fully.
There’s no reason to put off implementing the new security controls until the last minute, hoping that everything will be in order by then. You need to seek accurate information with respect to your current cybersecurity maturity stance and what you should start preparing for now. Implement these changes within your business immediately to ensure you will be ready for the changes to your eligibility as a contractor or supplier for the DoD and other federal entities.
We have highlighted some crucial aspects you must immediately focus on to remain eligible and in good standing with current regulatory requirements. In addition, we’ve also listed some strategic steps that you should immediately implement throughout your business to be ready for the enhanced cybersecurity practices required under the new CMMC 2.0 framework.
The DFARS Interim Rule
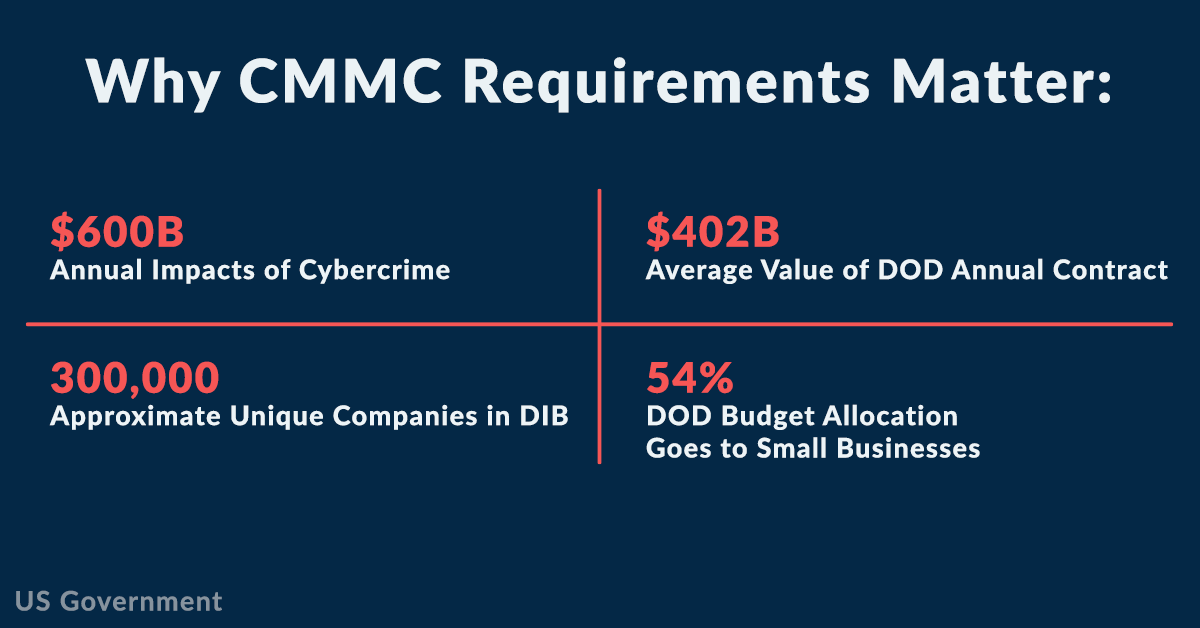
Since new requirements under CMMC 2.0 will not be fully rolled out for years, the Defense Federal Acquisition Regulation Supplement (DFARS) Interim Rule was established. The Interim Rule immediately establishes the DoD Assessment Methodology to get a measure of a contractor’s implementation of the existing cybersecurity requirements. According to DFARS Case 2019-D041, effective November 30, 2020, the Interim Rule requires all DoD prime contractors and the estimated 300,000+ DIB supply chain members to perform a minimal self-assessment of their current cybersecurity posture and document their results in the Supplier Performance Risk System (SPRS) at https://www.sprs.csd.disa.mil/.
All contractors and subcontractors with existing contractual obligations related to the NIST SP 800-171 framework standards must complete a self-assessment using the standard assessment and scoring methodology to assess their organization’s implementation of the NIST requirements. The assessment score must be uploaded to the federal Supplier Performance Risk System (SPRS) database to qualify for new or renewed defense contracts.
To help you better understand the DFARS Interim Rule requirements, you must familiarize your organization with these critical components:
- Self-assessment: It involves evaluating the implementation of 110 different cybersecurity controls defined by the NIST SP 800-171. Organizations must perform self-assessments using the new NIST (SP) 800-171 DoD Assessment Methodology.
- Scoring methodology: It begins with a “perfect” score of 110 for each NIST (SP) 800-171 control, that the organization must implement. Weighted points are deducted for every control that has not been implemented. Each deduction holds a point value ranging from one to five based on the individual control’s importance. No credit is given for partially implemented controls, except for multifactor authentication and FIPS-validated encryption.
- Submission of the score: You must upload the self-assessment score to a governmental Supplier Performance Risk System (SPRS) database within 30 days of completing the assessment to qualify for new contracts and contract renewals.
- System Security Plan (SSP): It is a required document that contains thorough details of implemented NIST 800-171 controls such as operational procedures, organizational policies and technical components.
- Plan of Action and Milestones (POA&M): If you have not fully implemented any control, you must provide a POA&M document as an appendix explaining how you plan on addressing the deficiencies and by when you will complete the implementation. You can post updated scores once previously deficient controls have been addressed and remediated.
Eligibility to win all new federal or defense contracts issued after December 1, 2020, includes requirements with respect to the completion of the Interim Rule standards.
Immediate steps to take
If not already completed, your organization should prepare to conduct a thorough and accurate self-assessment to measure your cybersecurity posture score as soon as possible to ensure you are adequately securing and protecting your information assets. This is the first step in preparing for the enhanced cybersecurity requirements and certification process rolling out under the new CMMC framework. To ensure you don’t miss out on any new contracts or renewal opportunities, you need to start preparing and implementing the necessary security controls and policies now.
Here are some steps you need to take to prepare your organization right away:
- Establish a Systems Security Plan (SSP): Building an SSP will help you map your network and information assets (hardware and software) and will mark the beginning of you knowing how many controls (out of the 110) your business has implemented so far.
- Assess how you deal with controlled unclassified information (CUI): Ask yourself questions on how your business manages CUI — who accesses it, where CUI lives, how it is shared, etc.
- Conduct a DoD self-assessment: You can utilize a tool to conduct a self-assessment and obtain a score as per the NIST (SP) 800-171 DoD Assessment Methodology.
- Build a POA&M document: In this document, list all the steps you will take to mitigate the deficiencies that prevented you from getting a perfect score of 110 (along with estimated completion time).
- Upload the self-assessment score: Don’t forget to upload the results to the governmental SPRS database within 30 days of conducting the self-assessment.
- Document everything: This step is non-negotiable. Ensure you document every crucial aspect of your journey — from preparation to self-assessment and remediation.
The enhanced cybersecurity policies, controls and standards within the CMMC regulatory framework are vast and complex, making understanding your obligations and how or where to get started a daunting and overwhelming task.
Partnering with a specialist can help make the entire process less stressful and time-consuming. As a Managed Service Provider (MSP), we can provide you with the specialized tools and cybersecurity expertise you need to help you prepare for and implement the cybersecurity controls necessary to satisfy and validate compliance to the DFARS Interim Rule and new CMMC 2.0 requirements.
Article curated and used by permission